
Security researchers have discovered a new malware geared with modules that target Oracle Micros Hospitality RES 3700 point-of-sale systems, one of the most widely used management software in the hospitality industry.
Named ModPipe, the malware is a modular backdoor that can steal the passwords for the PoS system databases by decrypting them from Windows registry values.
Risky modules unknown
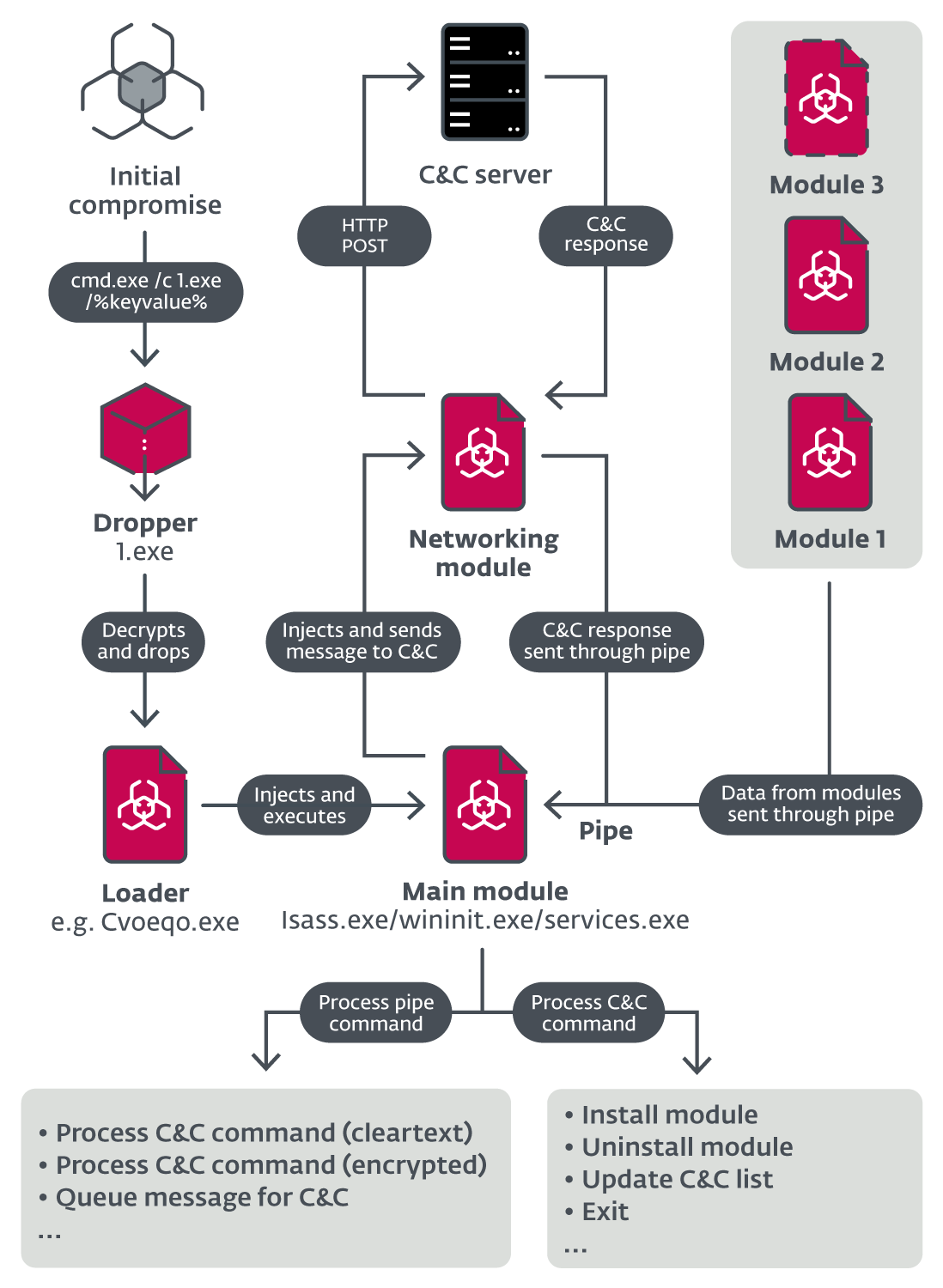
One particularity for ModPipe is its modular architecture that allows extending its features through downloadable components, such as GetMicInfo, used for decrypting database passwords.
Researchers at ESET found some basic ModPipe components at the end of 2019. In April 2020, they discovered in the wild three downloadable modules:
- GetMicInfo - steals database passwords, settings, and various data
- ModScan - runs scans on specified IP addresses
- ProcList - enumerates running processes and their modules
However, the list likely includes at least four more such components, albeit their function is currently unknown.
The researchers still don't know how tha malware compromises the PoS systems but they figured out its architecture, which includes an initial dropper, a persistent loader, the main module, a networking module, and downloadable components.
In a report shared with BleepingComputer, ESET says that GetMicInfo relies on a custom algorithm to intercept and decrypt the PoS database passwords.
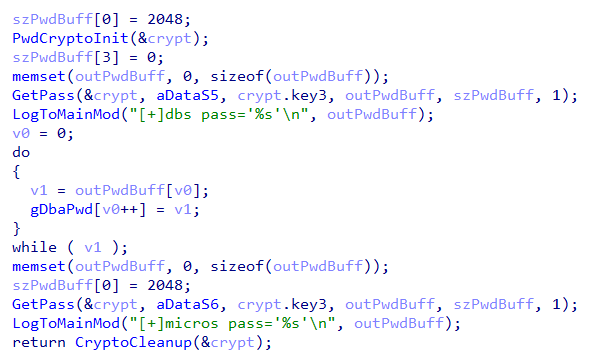
Details about the decryption mechanism are not public, suggesting that the threat actor may have reversed engineered the software for Oracle’s MICROS RES 3700 Restaurant POS System to understand how the passwords are encrypted and decrypted.
Alternatively, they could have gotten the info from a 2016 data breach that affected Oracle’s Micros PoS division, or by buying the code on a cybercriminal market.
Although the PoS databases contain sensitive information, simply accessing them with the stolen passwords does not mean that payment card data is at risk.
PoS systems store the most important card data (numbers, expiration dates) in an encrypted form, which means that the attacker also needs a way to learn the passphrase that generates the database encryption key.
“This process would then have to be implemented into the module and – due to use of the Windows Data Protection API (DPAPI) – executed directly on the victim’s machine” - ESET
The researchers believe that there may be another module that allows the decryption of the databases being stolen in the process:
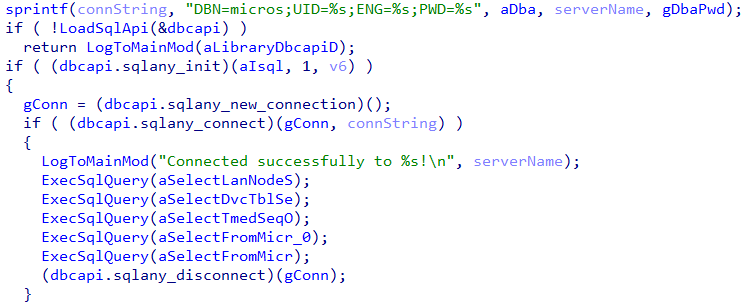
ModScan, the second module ESET analyzed, gathers info about the Micros PoS environment by scanning IP addresses specified in traffic from the command and control server.
Depending on the parameters received with the scan command, the malware may collect the following information about the system:
- version of the Oracle Micros RES 3700
- name of the database
- database server data
The third module, ProcList, has a simple task: get information about currently running processes. The details include name, the process identifier (PID), parent process PID, number of threads, token owner, token domain, process creation time, and command line.
ESET's report provides technical analysis of all three downloadable modules found as well as ModPipe's basic components.
Break down IAM silos like Bitpanda, KnowBe4, and PathAI
Broken IAM isn't just an IT problem - the impact ripples across your whole business.
This practical guide covers why traditional IAM practices fail to keep up with modern demands, examples of what "good" IAM looks like, and a simple checklist for building a scalable strategy.









Comments
Richard1572 - 5 years ago
Is there a Micros patch and or will a traditional Anti Virus catch the issue if its up to date?