
Threat actors have started to hunt for servers running Oracle WebLogic instances vulnerable to a critical flaw that allows taking control of the system with little effort and no authentication.
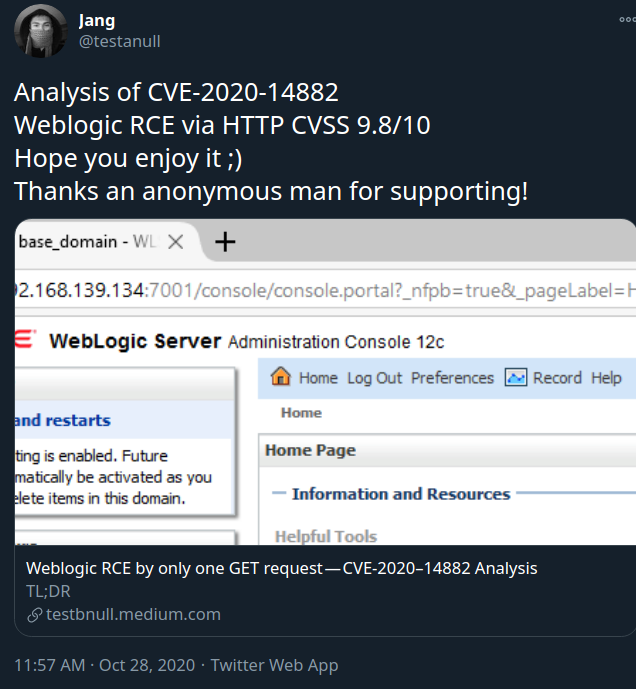
The vulnerability leveraged in the attacks is CVE-2020-14882 with a severity rating 9.8 out of 10 that allows compromising systems via a simple HTTP GET request.
Looking for targets
Oracle fixed the vulnerability in this month’s release of Critical Patch Update (CPU), crediting security researcher Voidfyoo of Chaitin Security Research Lab for finding and reporting it.
Honeypots set up by the SANS Technology Institute caught the attacks shortly after exploit code for CVE-2020-14882 emerged in the public space. Vulnerable versions of Oracle WebLogic Server are 10.3.6.0.0, 12.1.3.0.0, 12.2.1.3.0, 12.2.1.4.0 and 14.1.1.0.
In an advisory today, Johannes Ullrich, Dean of Research at SANS, says that exploit attempts on the honeypots came from the following IP addresses:
- 114.243.211.182 - assigned to China Unicom
- 139.162.33.228 - assigned to Linode (U.S.A.)
- 185.225.19.240 - assigned to MivoCloud (Moldova)
- 84.17.37.239 - assigned to DataCamp Ltd (Hong Kong)
Most of them are just pinging targets but the one from MivoCloud attempts to execute the “cmd /c” command, which runs the command specified in the string and then terminates.
SANS Institute is in the process of alerting the corresponding internet service providers of the offensive activity from the IP addresses above.
Ullrich says that the exploit attempts recorded by the honeypots just check if the system is vulnerable. SANS cannot provide details for the follow-up requests because the trap systems are configured not to reply with a correct response.
According to Ullrich, the exploit used in these attacks seems to be based on the technical details in a blog post (Vietnamese) published yesterday by security researcher Jang.
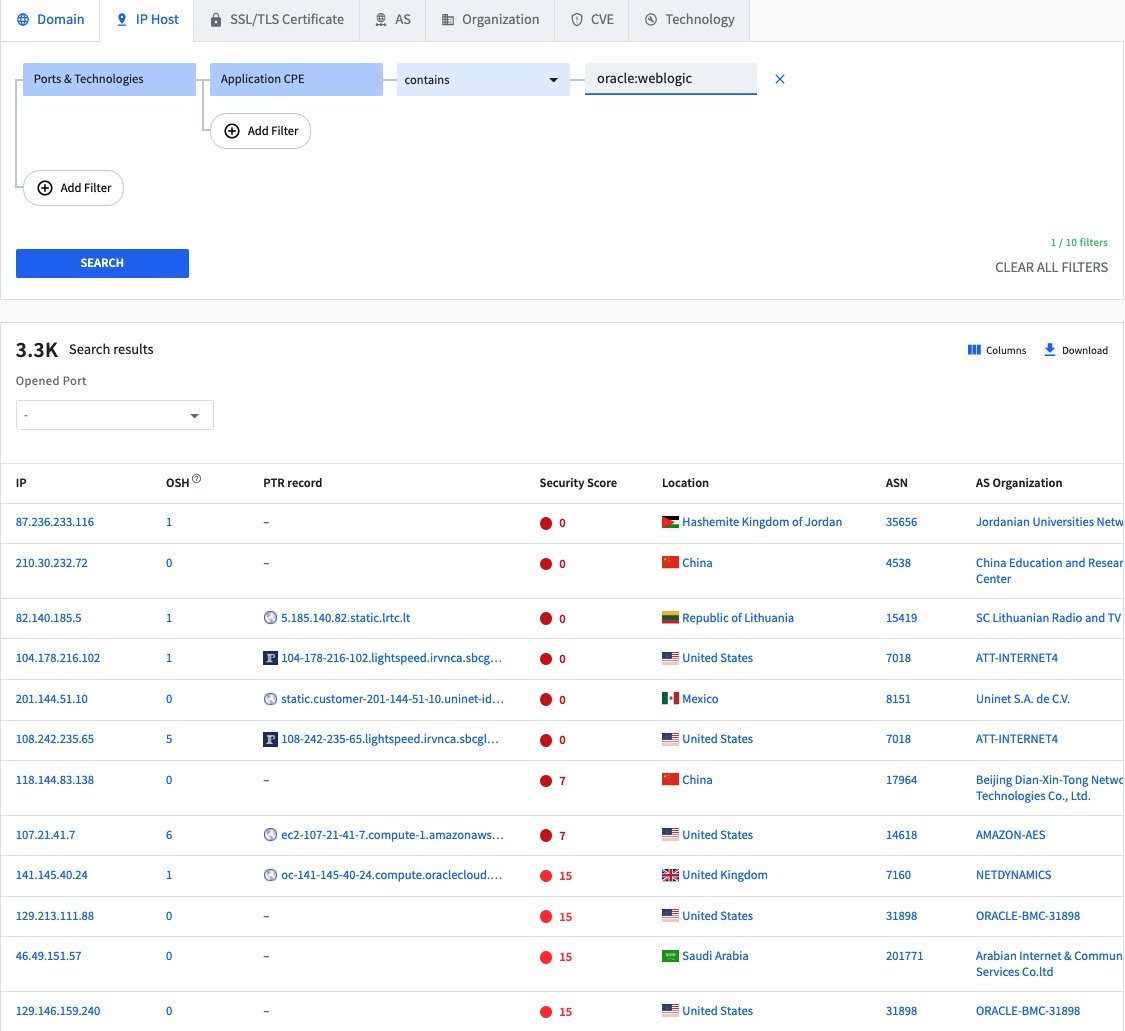
A search on Spyse engine for scanning and collecting reconnaissance information from exposed assets shows that there are more than 3,000 Oracle WebLogic servers reachable over the public internet and potentially vulnerable to CVE-2020-14882.
The attacks observed by SANS come a little over a week after Oracle released a patch for CVE-2020-14882. This should come as no surprise, though, considering how trivial it is to exploit, its critical severity, and that exploit code is publicly available. Applying the patch is currently the best solution to protect against these attacks.
Break down IAM silos like Bitpanda, KnowBe4, and PathAI
Broken IAM isn't just an IT problem - the impact ripples across your whole business.
This practical guide covers why traditional IAM practices fail to keep up with modern demands, examples of what "good" IAM looks like, and a simple checklist for building a scalable strategy.









Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now