
A suspected GandCrab Ransomware member was arrested in South Korea for using phishing emails to infect victims.
The GandCrab ransomware operation started in January 2018 when it quickly became a malware empire threatening businesses worldwide.
Operated as a Ransomware-as-a-Service (RaaS), the GandCrab developers teamed up with affiliates in a revenue share partnership, with affiliates earning between 70-80% of a ransom payment.
The operation shut down in the summer of 2019, but many security researchers believe the core developers went on to start the REvil ransomware group.
Suspected affiliate arrested in South Korea
As first reported by TheRecord, a 20-year-old man was arrested on February 25th by South Korean police after an international investigation traced GandCrab ransom payments to withdrawals made by the suspect.
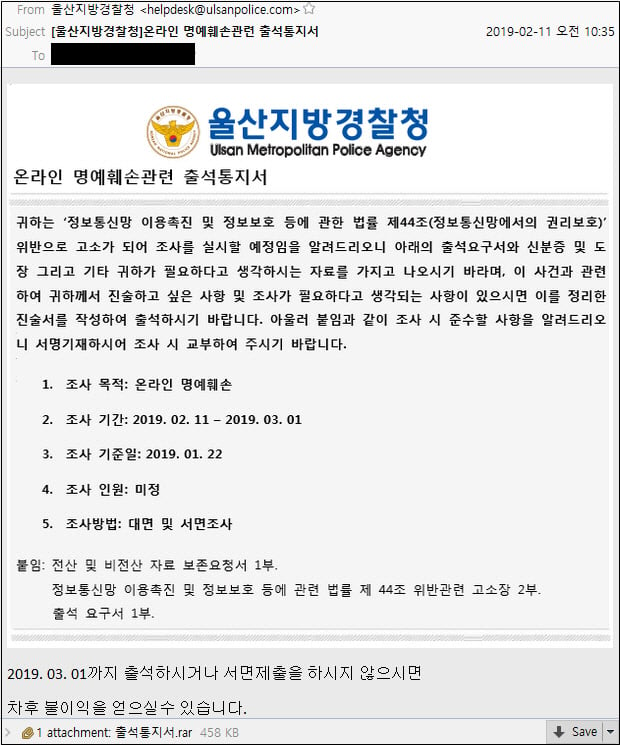
South Korean media states the suspect distributed 6,486 phishing emails. These emails pretended to be from South Korean police investigating the email recipient's online defamation.
Included in the emails were attachments that would infect the victim with the GandCrab ransomware, encrypt files, and demand a $1,300 bitcoin ransom.
While the GandCrab operators boasted that they generated $2 billion in ransom payments, this alleged member did not get rich from his illicit activities.
South Korean police state that the suspect only earned 12 million South Korean won or approximately $10,500 as part of the illicit activities.
The police state that another suspect, who shared the GandCrab ransomware with the arrested individual, is still at large.
In July, Belarus law enforcement also arrested a 31-year old GandCrab member who acted as an affiliate for the ransomware operation.
Joint law enforcement operations have had already had great success battling ransomware gangs this year. Last month, international law enforcement took down Netwalker and the Egregor ransomware operations.
Break down IAM silos like Bitpanda, KnowBe4, and PathAI
Broken IAM isn't just an IT problem - the impact ripples across your whole business.
This practical guide covers why traditional IAM practices fail to keep up with modern demands, examples of what "good" IAM looks like, and a simple checklist for building a scalable strategy.








Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now